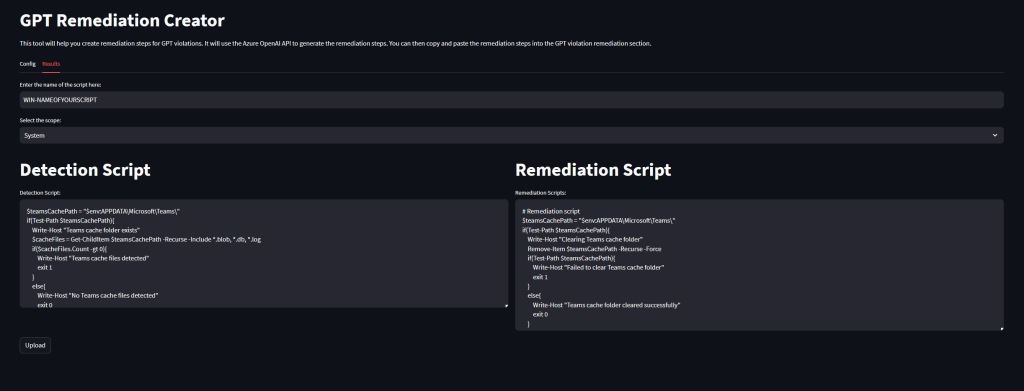
Remediations play a pivotal role in effective client management, allowing organizations to proactively identify and resolve end-user issues. Additionally, they serve as a valuable tool for enforcing specific settings or configurations that may not be natively supported in Microsoft Intune. However, the process of crafting these scripts can often be intricate and time-consuming.
Imagine a solution where you can simply describe your desired configurations, and a tool generates the necessary scripts for you. If you find this idea appealing and are keen to explore such a solution, this blog is tailored to meet your exact needs.